Rob
Well-Known Member
Have you heard about California Civil Code Title 1.81.26, Security of Connected Devices?
Pathway Connectivity, a division of Acuity Brands, is prepared. Read all about it here.
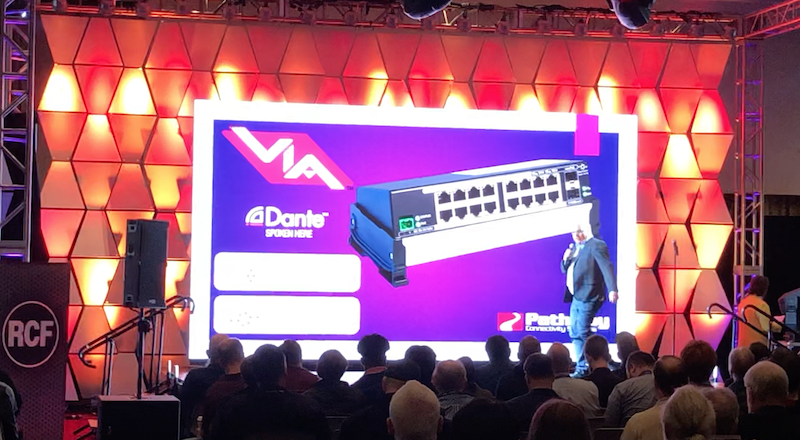
This light-hearted video from the #LDI New Product Breakfast introduces security measures that we have implemented to protect your products and production.
Pathway Connectivity, a division of Acuity Brands, is prepared. Read all about it here.
This light-hearted video from the #LDI New Product Breakfast introduces security measures that we have implemented to protect your products and production.